In the modern digital age, the technological landscape must keep evolving to protect the data infrastructure from an ever-increasing onslaught of security threats. The Center for Internet Security (CIS) controls are a perfect starting point for any organization looking to strengthen its cyber defense.
A condensed list of high-priority and highly effective defensive measures, these best practices, created by the SANS Institute (and known as the SANS Critical Controls), are essential to all sizes of organizations. Implementing these protective protocols can stop the most pervasive and dangerous cyber attacks.
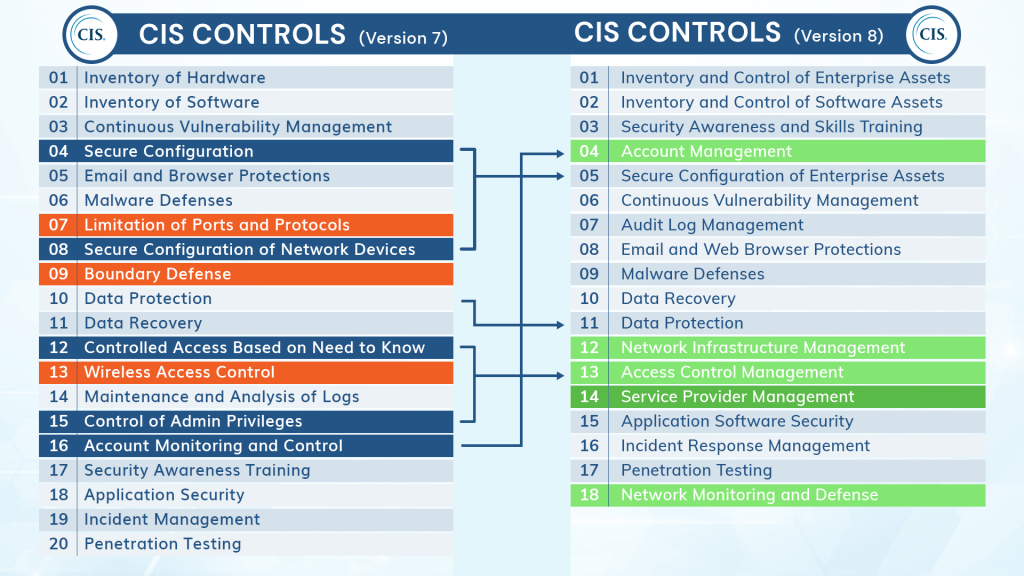
The CIS Controls in version 8 include notable improvements from version 7, with 18 critical controls instead of 20. In this blog, we will outline the 18 critical controls mentioned in CIS v8 and discuss how it has helped increase IT systems and data infrastructure safeguarding.
What are the 18 Critical Controls Outlined in CIS V8?
The latest version of the CIS Controls, version 8, has 18 critical controls enumerated in it and has been modified based on tasks and combined by activities.
CIS Control 1: Inventory and Control of Enterprise Assets
The first step in minimizing your organization’s attack surface is to understand all the devices connected to it thoroughly. Ensure all your gear is present and accounted for using active and passive asset discovery tools to track your inventory continuously.
CIS Control 2: Inventory and Control of Software Assets
Asset detection is also addressed by one of the top controls, making network inventorying the single most important step you can take to harden your system. After all, you can’t keep track of resources on your network that you are unaware of.
CIS Control 3: Data Protection
The responses to these inquiries are included with the policy selections and incident response processes in a thorough data management plan. The cornerstones of such a plan are being aware of what data a company creates or consumes and being able to classify it according to sensitivity. Despite having a straightforward name, this control is among the more intricate and challenging to implement due to continuing procedures like storing sensitive information.
CIS Control 4: Secure Configuration of Enterprise Assets and Software
File integrity monitoring (FIM) is typically used to monitor master images, configuration files, etc. This control emphasizes automating configuration monitoring systems to send security alarms if known baselines are deviated from. Mobile devices, laptops, workstations, servers, and other devices are among the systems that fall under the purview of this control.
CIS Control 5: Account Management
Most organizations have a system in place to govern authentication techniques if you want to prevent legitimate credentials from falling into the hands of hackers. Cybercriminals frequently target administrative credentials. Fortunately, you can take several measures to protect them, such as maintaining a thorough list of admin accounts and altering default passwords. It is significantly more difficult for hostile actors to successfully assault a business and steal or destroy assets when accounts are monitored and controlled.
CIS Control 6: Access Control Management
Inventorying your network’s wireless access points is the initial stage in applying this control. The control then delves deeply into reducing all possible dangers associated with wireless access. You can also mitigate potential security problems when data privileges are extremely lenient by encrypting information in transit and preventing connectivity between workstations.
CIS Control 7: Continuous Vulnerability Management
Keeping up with all the common vulnerabilities and exposures (CVEs) discovered in real time around the globe is a significant difficulty in cybersecurity. Effective security programs must address a constant stream of brand-new vulnerabilities. CIS cites continuous vulnerability assessment and remediation as crucial component of risk and governance programs.
CIS Control 8: Audit Log Management
System logs give a precise description of all network events. Therefore, in a cybersecurity incident, good log management procedures will provide you with all the information you require regarding the who, what, where, when, and how of the incident. Security teams must monitor logs and use tools that can analyze log data and produce management advice that can be implemented.
CIS Control 9: Email and Web Browser Protections
Email and online browsers present more security risks than phishing alone. Cybercriminals may be able to use even a single pixel from an email image to provide them with the information they require to launch an attack. Attackers routinely use web browsers and email clients as entry points for code exploitation and social engineering. Hence safeguards must be put in place to prevent interactions with untrusted environments.
CIS Control 10: Malware Defenses
Organizations must strengthen their malware defenses in response to the rising number of ransomware assaults. Ensure the rest of your security toolchain works properly with your antivirus software. Install anti-malware software and make sure it is maintained up to date. To exercise this control, specific features like auto-run and auto-play for removable media must be disabled.
CIS Control 11: Data Recovery
In the event that preventive procedures are unsuccessful, organizations must have a solid plan in place for recovering lost data. Are you running automated backups regularly? Do you safeguard the data you have backed up? You will be protected from dangers like ransomware with adequate data recovery capabilities. To be ready in the event of actual data loss, it is also crucial to practice and test data restoration.
CIS Control 12: Network Infrastructure Management
Utilizing this control will enable you to lessen your attack surface using techniques like application firewalls and automatic port scanning. Whether real or virtual, network devices can be considered the entrances to your company. To manage ingress and egress filtering rules for enterprise policy-based protection, routers, switches, firewalls, and other network devices must be properly configured and administered.
CIS Control 13: Network Monitoring and Defense
This control uses host-based intrusion detection systems, network intrusion detection systems, centralizing security event alerting, and more. Network defense and monitoring must be seen as a continual process that receives significant attention from security personnel. Networks will remain more resistant to attacks with the help of security measures like network segmentation and application layer filtering.
CIS Control 14: Security Awareness and Skills Training
Most organizations should prioritize security training more because of the growing cybersecurity skills gap. This control also highlights the necessity of continual security education instead of one-time engagements. Employees are significantly more resistant to phishing and social engineering attempts when they know how to practice strict cyber hygiene.
CIS Control 15: Service Provider Management
Most businesses commit a variety of tasks to outside service providers who usually have access to sensitive information. Sadly, service providers have evolved into a cybercriminal attack vector, making it necessary for your business to manage the security of its service providers. And this isn’t only for security’s sake—many compliance standards, like SOC 2, ISO 27001, HIPAA, and PCI, demand that third-party service providers be covered by compliance.
CIS Control 16: Application Software Security
Internally created code requires security assessments using static and dynamic security analysis techniques to find undiscovered flaws. Your application base is the most popular target for hackers, so building a thorough program of application security controls is crucial. This has to incorporate controls for the software development lifecycle (SDLC), testing, and scanning.
CIS Control 17: Incident Response Management
This control aids in developing tactics so that you are not caught off guard when cybersecurity incidents happen. Learn who in your organization addresses incidents and the procedures they’ll employ to reduce their impact. Conducting post-incident reviews is also essential if you want to comprehend what happened and figure out how to avoid it happening again.
CIS Control 18: Penetration Testing
Regular penetration testing lets you spot weaknesses and attack routes that might otherwise go undetected until they were used maliciously. It’s a crucial part of discovering and pinpointing potential major vulnerabilities in your organization’s internal or external networks, applications, or systems.
How Do the Changes in CIS V8 Improve Data Security?
Here is a comparison between the CIS V7 and V8 controls:
How do these changes impact the current data security requirements?
Simpler and more reliable
Every safeguard has been developed in a way that calls for the least amount of interpretation.
Each safeguard is created with an emphasis on quantifiable behaviors, specifies measurement as a step in the process, and is written in plain language to prevent repetition.
Task-based attention no matter who exercises controls
You may have noticed that CIS Controls Version 8 groups and combines controls based on activities rather than device management.
This results in reducing the number of Controls from 20 to 18, as defined boundaries, isolated islands of security implementation, and physical devices are no longer as significant.
Updated for relevance in the present cyber ecosystem
The CIS Controls V8 program is made to stay up to contemporary hardware and software.
The transition to cloud computing, mobility, outsourcing, work-from-home policies, virtualization, and evolving attacker strategies were the driving forces behind this. Therefore, whether you choose a cloud environment or a hybrid one, the new controls can better meet your organization’s security needs.
Implementation Group 1 (IG1) Definition
IG1 primarily outlines fundamental cyber hygiene while serving as an evolving benchmark for business information security. Consider it the basic set of cyber defense measures you can use to protect your systems from typical online threats.
IG1 is the on-ramp to the controls, whereas IG2 and IG3 build on earlier IDs.
In summary, CIS Controls can help you improve your organization’s security posture. Version 8 offers backward compatibility with older versions and an upgrade path for users of older versions to version 8.
CIS V8 Controls Compliance Certification With Akitra!
Establishing trust is a crucial competitive differentiator when prospecting new SaaS businesses in today’s era of data breaches and compromised privacy. Customers and partners want assurances that their organizations are doing everything possible to prevent disclosing sensitive data and putting them at risk, and compliance certification fills that need.
Akitra offers an industry-leading, AI-powered Compliance Automation platform for SaaS companies. Using automated evidence collection and continuous monitoring, together with a full suite of customizable policies and controls as a compliance foundation, our compliance automation platform and solutions help our customers prepare readiness for the CIS V8 Controls, along with compliance security frameworks like SOC 1, SOC 2, HIPAA, ISO 27701, ISO 27017, ISO 27018, PCI DSS, GDPR, NIST 800-53, NIST 800-171, CMMC, FedRAMP, and more such as CIS AWS Foundations Benchmark, etc. In addition, companies can use Akitra’s Risk Management product for overall risk management for your company, Trust Center, and AI-based Automated Questionnaire Response product to streamline and expedite security questionnaire response processes delivering huge cost savings. Our compliance and security experts will provide customized guidance to navigate the end-to-end compliance process confidently.
The benefits of our solution include enormous savings in time, human resources, and cost savings, including discounted audit fees with our audit firm partners. Customers achieve compliance certification fast and cost-effectively, stay continuously compliant as they grow, and can become certified under additional frameworks using a single compliance automation platform.
Build customer trust. Choose Akitra TODAY!
To book your FREE DEMO, contact us right here.








